CVE-2024-26152 DetailDescription### Summary On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability. ### Details Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1. ### PoC 1. Create a project.  2. Upload a file containing the payload using the "Upload Files" function.   The following are the contents of the files used in the PoC ``` { "data": { "prompt": "labelstudio universe image", "images": [ { "value": "id123#0", "style": "margin: 5px", "html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>" } ] } } ``` 3. Select the text-to-image generation labeling template of Ranking and scoring   4. Select a task 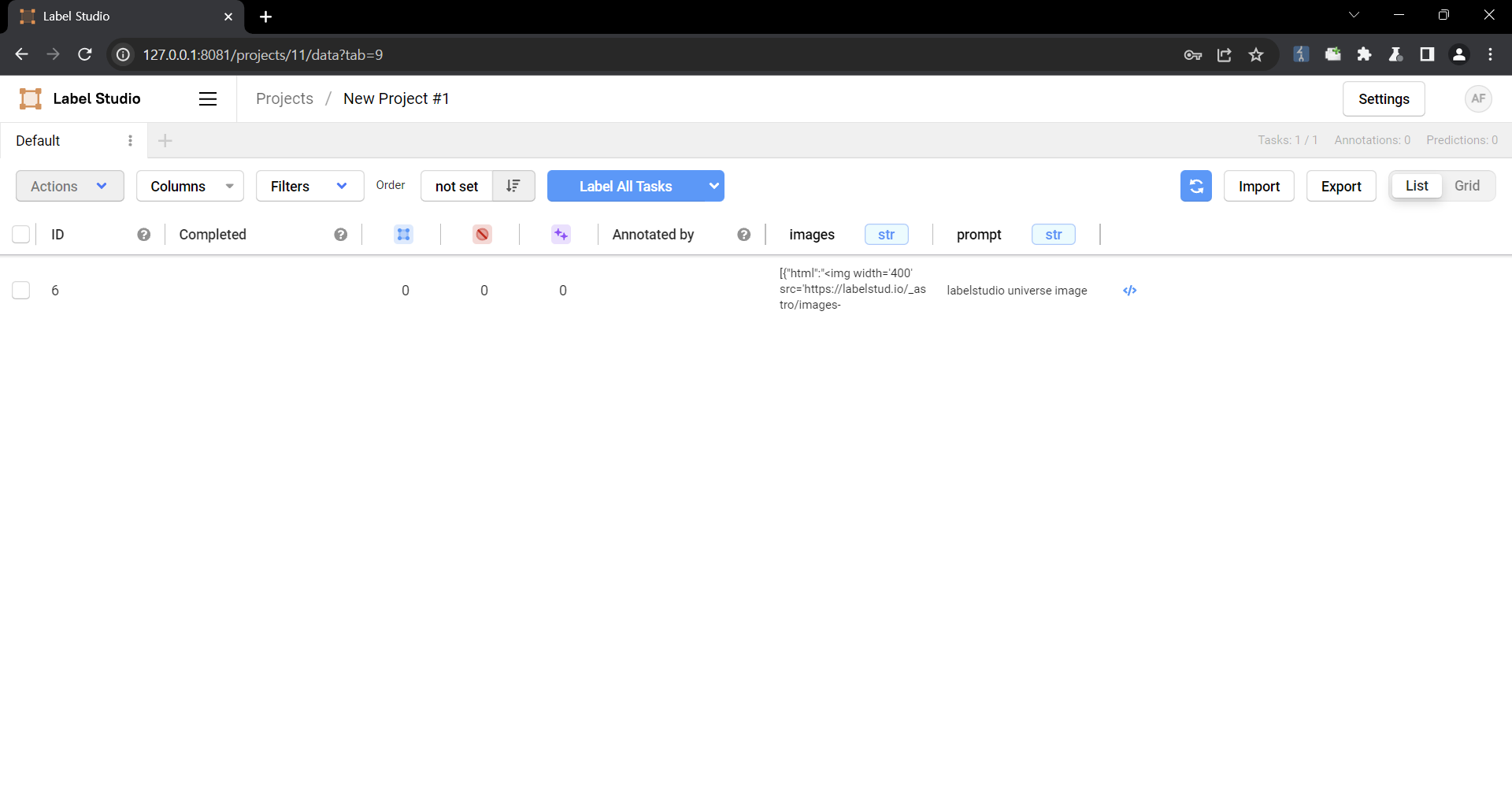 5. Check that the script is running 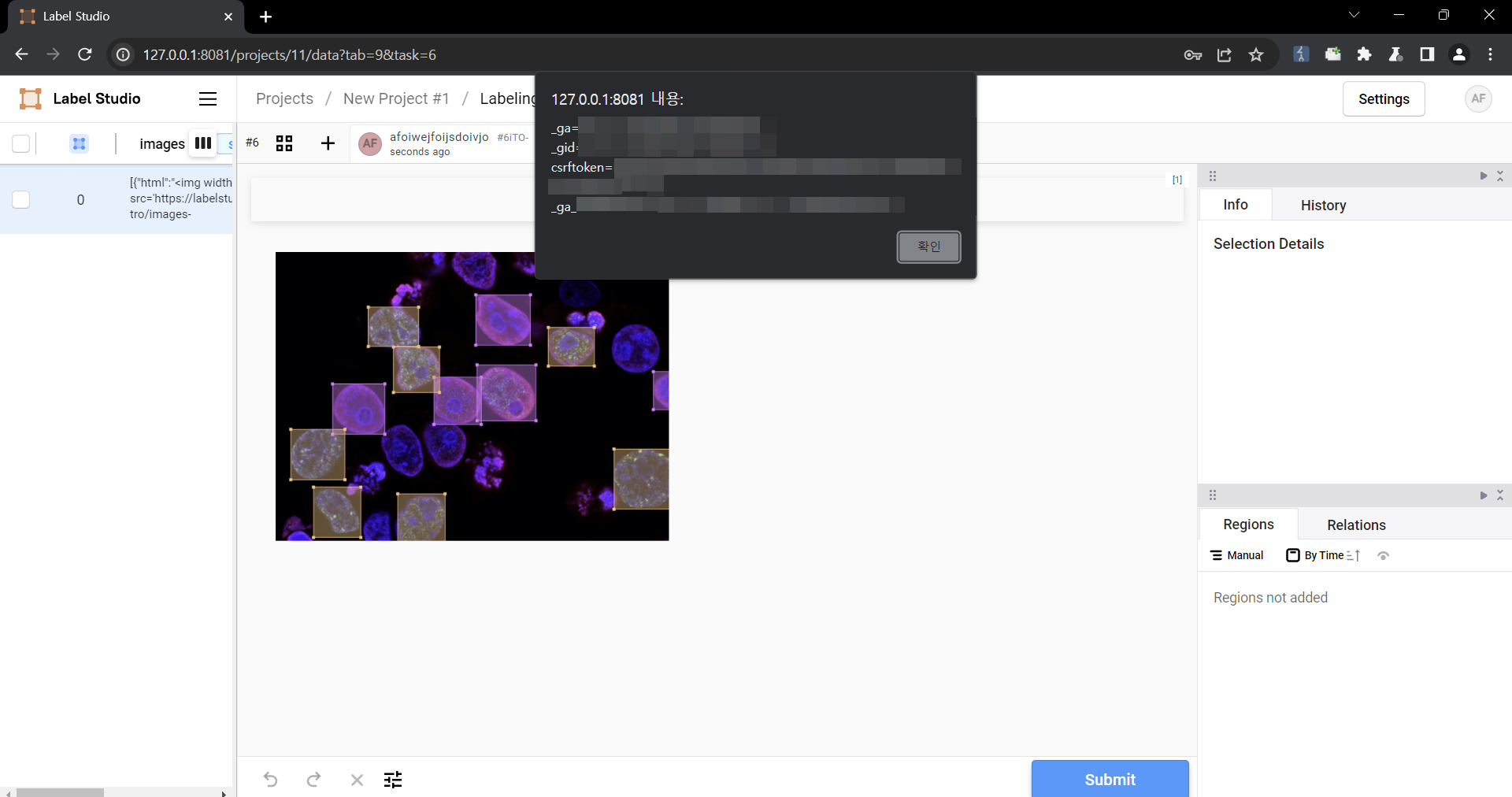 ### Impact Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering. Metrics
NVD enrichment efforts reference publicly available information to associate
vector strings. CVSS information contributed by other sources is also
displayed.
CVSS 4.0 Severity and Vector Strings:
References to Advisories, Solutions, and ToolsBy selecting these links, you will be leaving NIST webspace. We have provided these links to other web sites because they may have information that would be of interest to you. No inferences should be drawn on account of other sites being referenced, or not, from this page. There may be other web sites that are more appropriate for your purpose. NIST does not necessarily endorse the views expressed, or concur with the facts presented on these sites. Further, NIST does not endorse any commercial products that may be mentioned on these sites. Please address comments about this page to [email protected].
Weakness Enumeration
Known Affected Software Configurations Switch to CPE 2.2CPEs loading, please wait.
Denotes Vulnerable Software Quick InfoCVE Dictionary Entry:CVE-2024-26152 NVD Published Date: 02/22/2024 NVD Last Modified: 05/16/2025 Source: GitHub, Inc. |
||||||||||||||||||||||
You are viewing this page in an unauthorized frame window.
This is a potential security issue, you are being redirected to https://nvd.nist.gov
 An official website of the United States government
An official website of the United States government
Official websites use .gov
A .gov website belongs to an official government organization in the United States.
Secure .gov websites use HTTPS
A lock (


